
Legacy Downtime costs $9,000/min. Are you protected?
Get a Free Assessment
 What is hardware virtualization and its benefits for legacy systems?
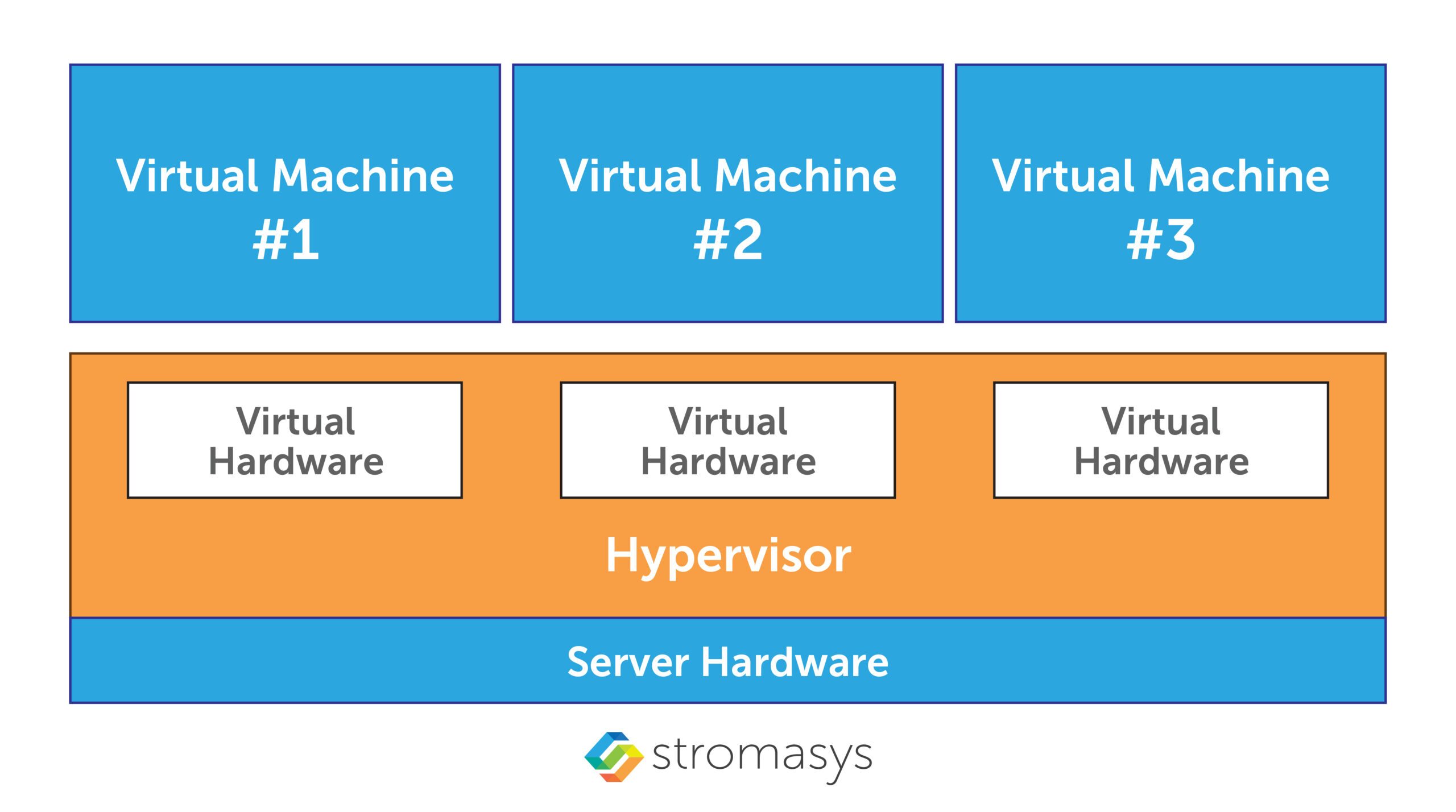
What is hardware virtualization and its benefits for legacy systems?Hardware virtualization is a technology of creating multiple virtual host environments on a single physical machine. These multiple environments are called virtual machines (sit between the hardware and the guest operating system), allowing multiple operating systems to run independently as if they have their own dedicated hardware.
For businesses dependent on legacy applications, hardware virtualization solves a critical problem. You can run multiple workloads on a virtual host without depending on the legacy hardware. This not only reduces the risks linked to outdated hardware but also optimizes resource usage.
 Articles
ArticlesG2 reports that companies using virtualization see a 50% jump in operational efficiency. Even more impressive, 66% of businesses experience greater agility after making the switch.
But here’s the reality for companies running legacy systems. Finding replacement parts for aging hardware is getting harder. What happens when a critical component fails? The risk is real, especially when mission-critical applications depend on that hardware.
Hardware virtualization offers a practical solution. It lets you move existing workloads to virtual machines without changing your applications. Your legacy software runs unchanged on modern infrastructure.
So, for IT teams managing legacy infrastructure, virtualization simplifies daily operations. Administrative tasks become less complex. Maintenance headaches decrease.
Here, you will learn in detail about hardware virtualization and then discover how it can bridge the gap between your reliable legacy applications and modern servers.
Legacy Hardware Virtualization, often known as just virtualization, is the process of abstracting computer resources from the software that uses them. Put simply, a single physical machine is divided to act like multiple virtual machines (VM).
Virtual machines function independently, each with its own OS and applications. They behave like standalone computers.
This single host system can support multiple virtual environments, each functioning independently while sharing the same architecture. As a result, businesses can run various applications or even different operating systems on one server seamlessly. This is achieved through software called Hypervisor.
Getting the hang of virtualization can be pretty easy. Let’s break it down for you:
A hypervisor is the underlying technology that decouples hardware from software. It allows multiple VMs to operate on a single physical server – each with its own operating system and resources. This setup lets you install software on these VMs just as you would on any standard computer.
The hypervisor serves as a bridge. It connects virtual machines to the physical hardware and manages resources efficiently. The physical server is the host, and the virtual environments are guests.
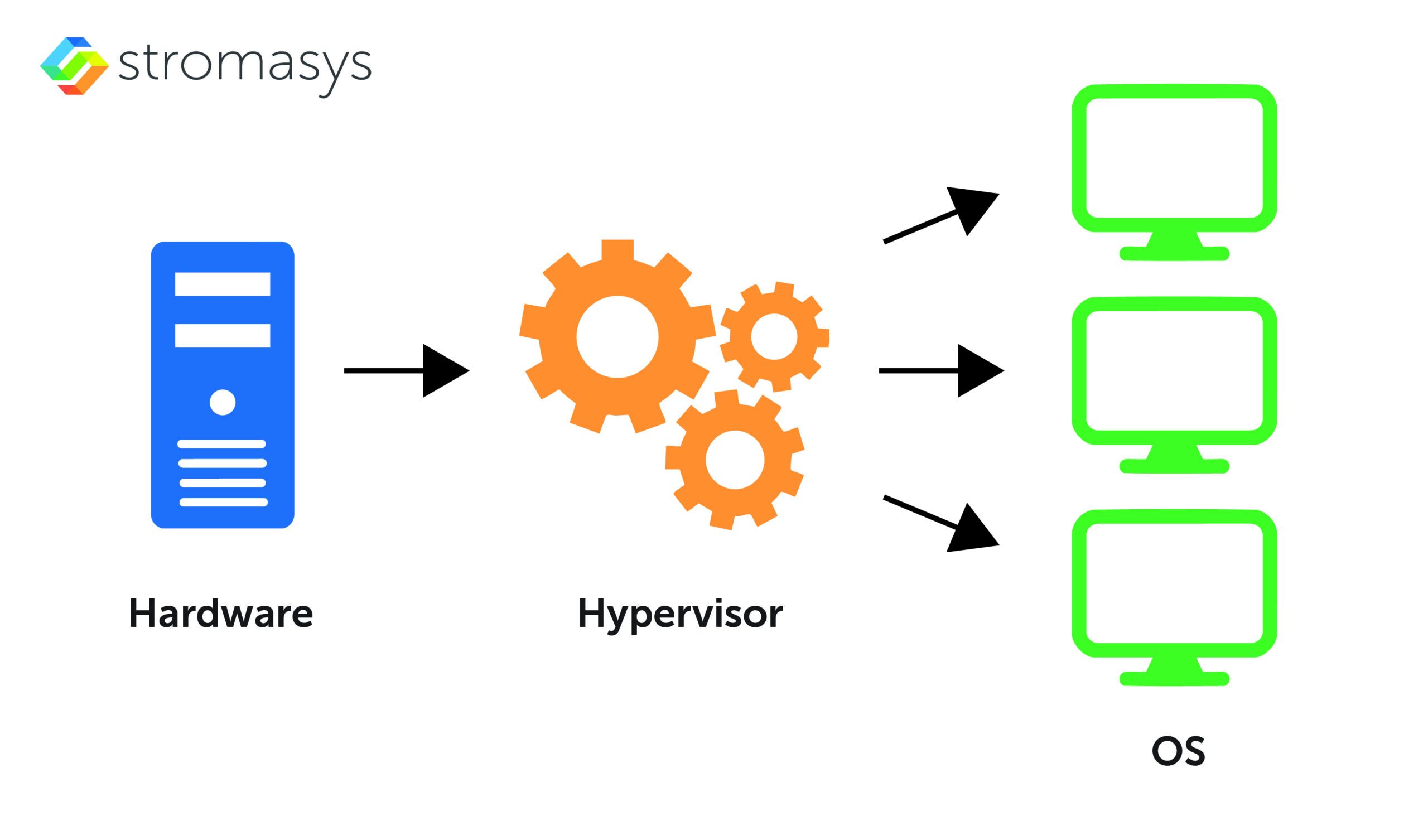
Once installed on a server, the hypervisor efficiently handles virtual machines by loading their images. It directs requests for processing power, memory, and storage to the host using API calls. This ensures smooth data exchange between applications.
Hypervisors are categorized into two types:
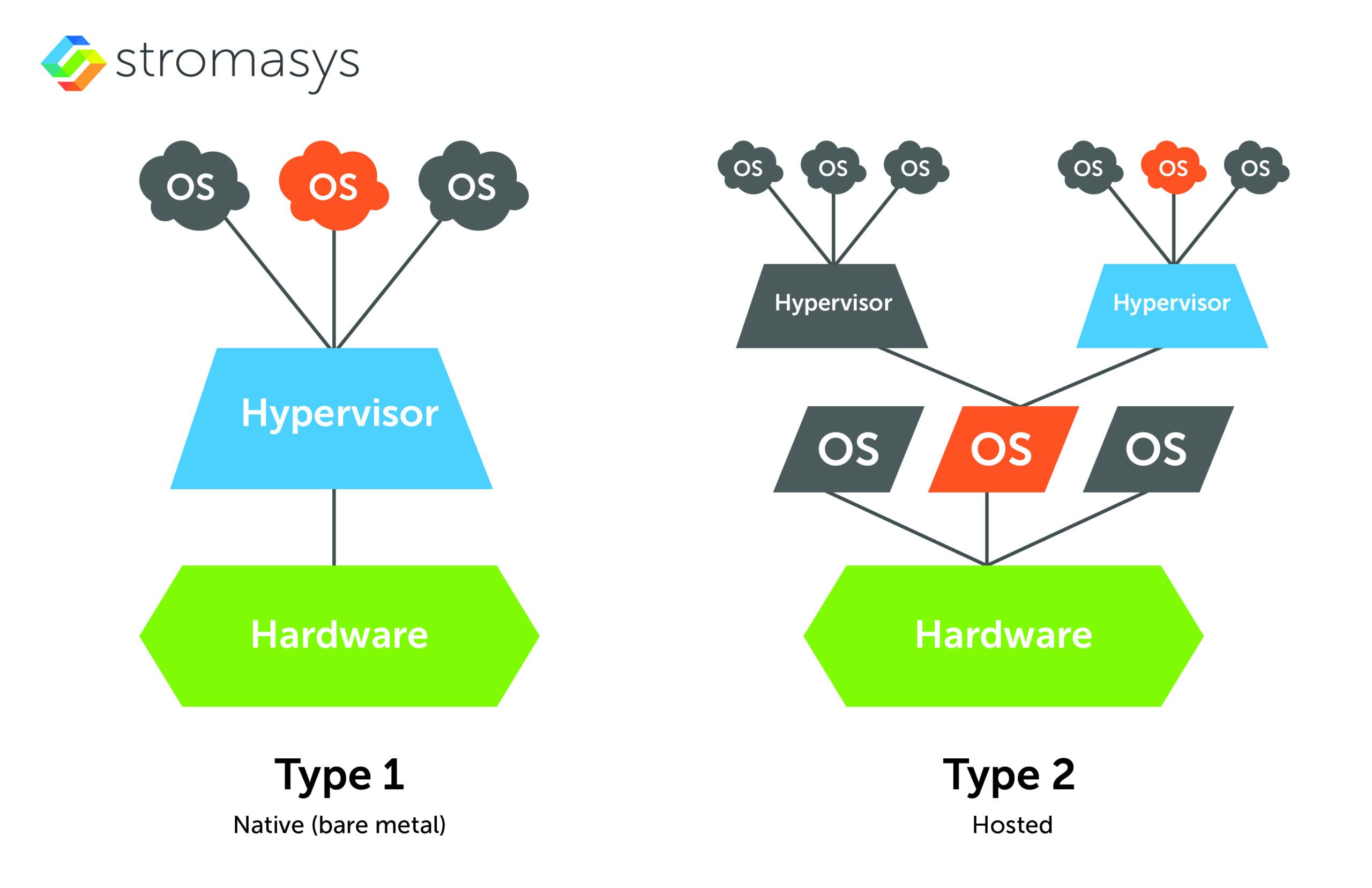
Understanding the differences between these two helps in choosing the right solution for your infrastructure needs.
| Attribute | Type 1 Hypervisors | Type 2 Hypervisors |
|---|---|---|
| Working principle | Installs directly on server hardware, providing a layer of abstraction between the physical hardware and virtual machines. | Installs on top of a host operating system, allowing it to manage and run multiple virtual machines. |
| Also known as | Bare-metal hypervisor. | Hosted hypervisor. |
| Resource Access | Direct access to hardware. | Negotiates with host OS. |
| Ideal Use Cases | Production servers, high workloads. | Development, testing, desktops. |
| Complexity | Requires admin-level knowledge. | Easier to use, basic knowledge. |
| Examples | VMware ESXi, Hyper-V, KVM. | VirtualBox, VMware Workstation Player, Virtual PC. |
It’s no secret that keeping an outdated thing is costly and risky. Legacy hardware is no exception. Let’s explore the reasons that make hardware virtualization evident.
The methods vary in approach and abstraction levels, but they share common goals. Here’s a breakdown of the most popular techniques:
This method completely virtualizes the physical server and creates virtual environments that behave like standalone servers. Applications and operating systems run unchanged in this setup, as if on dedicated hardware.
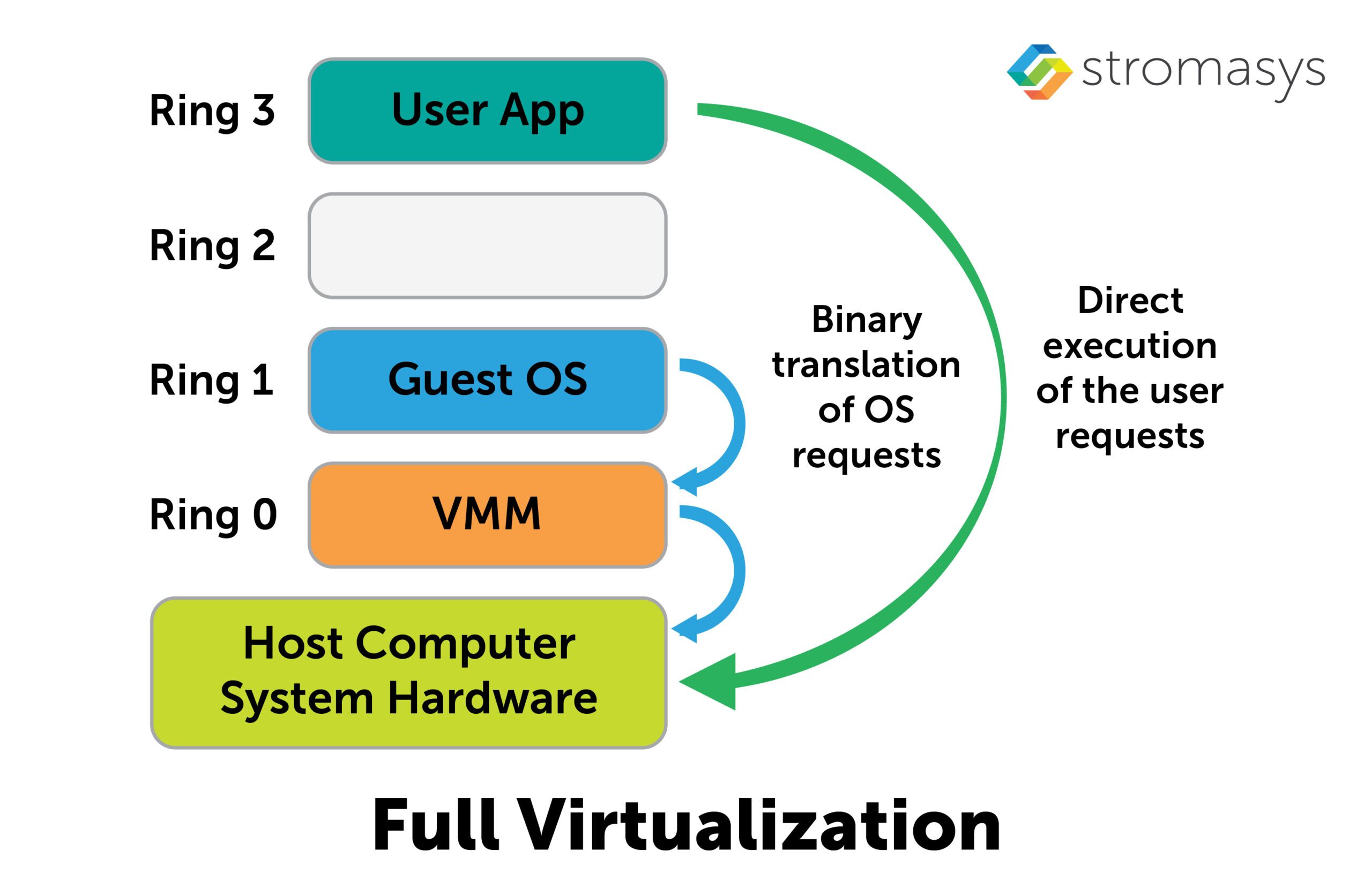
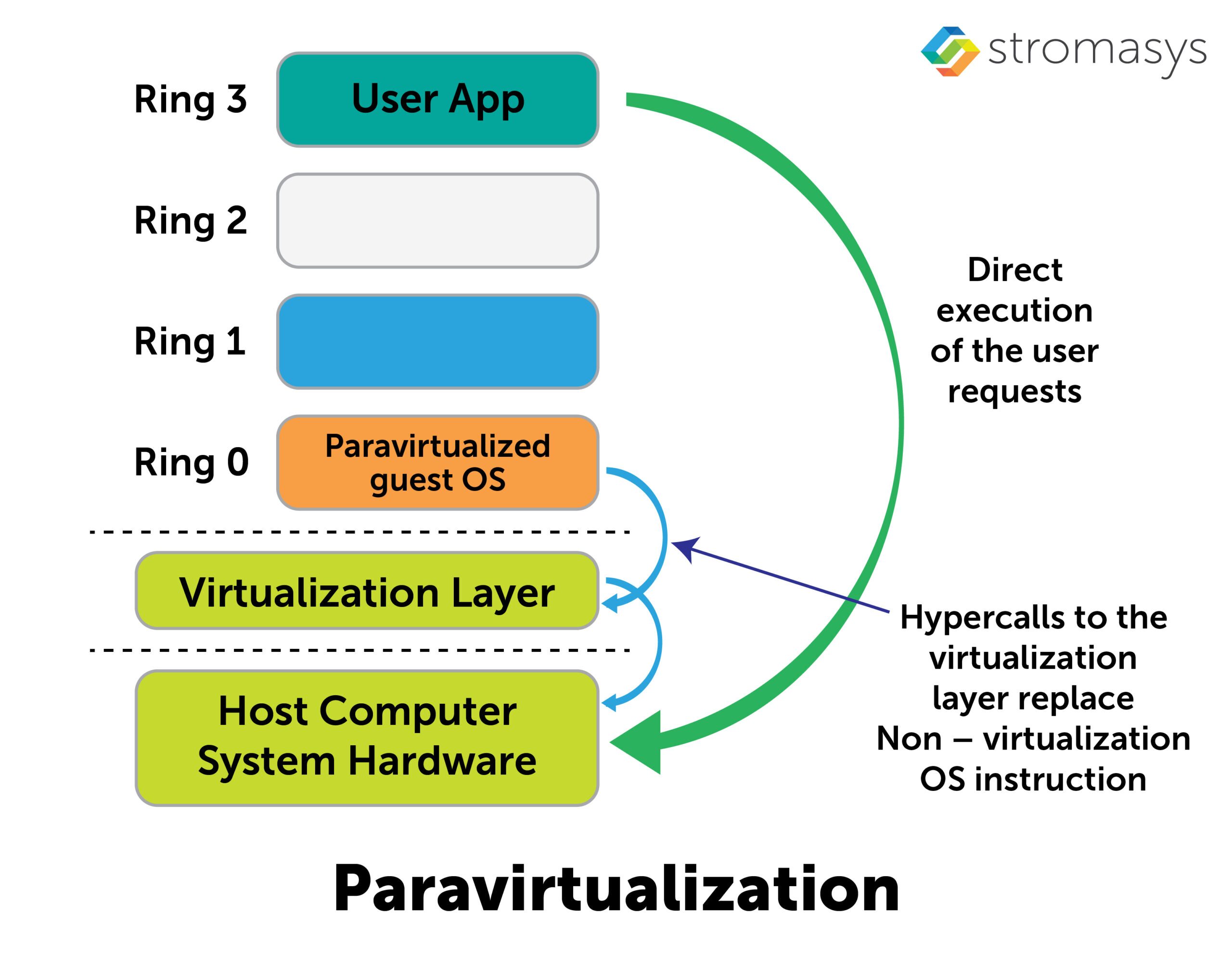
This technique uses modified operating systems that are aware of the virtualized environment. Unlike full virtualization, no hardware simulation takes place. Instead, it uses an application programming interface (API) to bridge the interaction between the guest OS and the hypervisor.
The guest OS is modified to include custom instructions, called hypercalls, that work with the hypervisor through APIs. These hypercalls manage key tasks like memory operations, and the OS is rebuilt to run in the para-virtualized setup.
This technique leverages a computer’s hardware to support and manage fully virtualized virtual machines (VMs). Introduced by IBM in 1972 with the System/370, it addressed the inefficiencies of software-based virtualization.
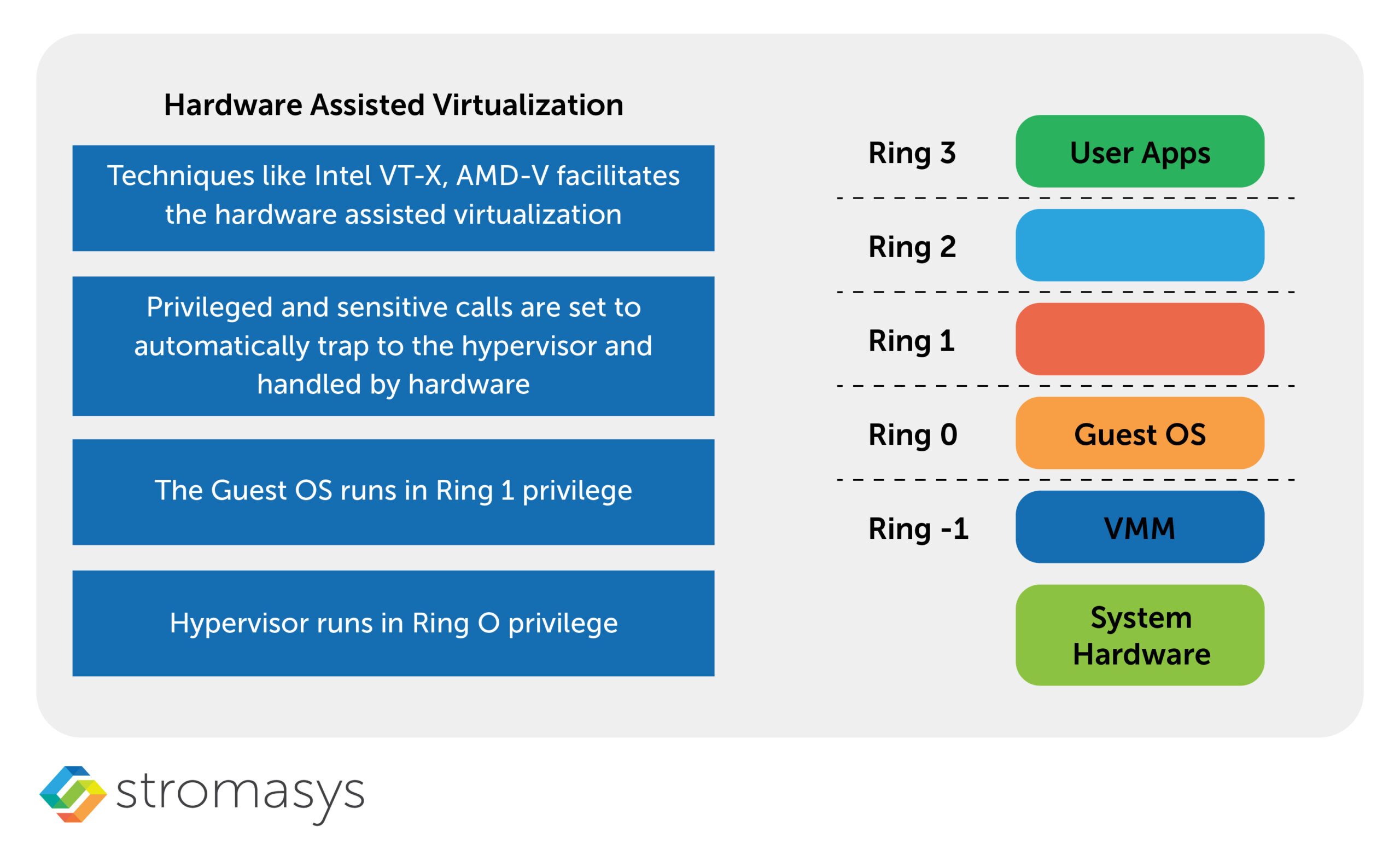
It uses processor extensions like Intel VT and AMD-V to optimize virtualization tasks. The hypervisor communicates directly with the hardware, which handles the complex processes of VM creation and management.
This approach isolates multiple applications and OS instances on the same server. It ensures security and seamless resource sharing across environments.
Legacy Hardware virtualization offers many advantages. Understanding these can clarify how it benefits your organization, especially if you are dealing with legacy systems.
The real-world use cases of legacy hardware virtualization are as follows:
Having said that hardware virtualization has a multitude of use cases – it’s relevance in optimizing mission-critical workloads is more than you can imagine.
Being a pioneer in hardware emulation, Stromasys combines it with virtualization, prolonging the lifespan of legacy software. We have meticulously engineered our Charon emulation software that not only eliminates the risk but also extends the lifespan of your business applications – more reliably than ever before.
Having said that hardware virtualization has a multitude of use cases – it’s relevance in optimizing mission-critical workloads is more than you can imagine.
Being a pioneer in Legacy hardware virtualization, Stromasys makes this journey easier. We have meticulously engineered our Charon emulation software that not only eliminates the risk but also extends the lifespan of your business applications – more reliably than ever before.
Here is how we combine emulation and virtualization and create a seamless environment that run critical workloads efficiently:
1) Physical hardware: your physical computer runs a hypervisor such as VMware ESXi. This is the virtualization host system.
2) Virtualization: you configure a virtual machine with sufficient resources to run an emulator. On this virtual machine you install an operating system supported by the desired emulator software (e.g., Red Hat Linux or Rocky Linux). This virtual hardware is your emulator host system.
3) Emulation: you install and configure the desired emulator software on the emulator host. The emulated legacy hardware is the emulator guest system.
4) Migration: operating system and applications are migrated from the legacy physical hardware into the emulator guest system.
5) Outcome: The legacy OS and applications in the emulator run as they normally would. The instructions they use are translated by the emulator to the instructions of the Linux emulator host system. The actions of the Linux system are mapped by the hypervisor to the actual resources of the physical hardware.
Eliminate concerns about
legacy hardware malfunctions. Virtualize them with Stromasys Charon today!
They are full virtualization, partial virtualization, and paravirtualization:
Yes, it is usually safe and useful. Once you enable it, you can run virtual machines for testing and running different OS for making the most out of your hardware.
In general, people tend to use Hardware Virtualization, Server virtualization, and Virtualization interchangeably all the time. Basically, they refer to the same thing.
Type 2 virtualization is where a hypervisor does not run on the hardware but consists of running as a program on an existing operating system. It is also known as a “hosted hypervisor”. It’s great for running more than one OS on a desktop or notebook.
Sanjana Yadav is a versatile content writer with a strong passion for exploring trending technologies and digital trends. Driven by curiosity for industry innovations, she specializes in transforming complex concepts into engaging and compelling narratives that drive results and help brands connect with their audiences and achieve their business objectives.
The corporate IT landscape is evolving rapidly, presenting significant challenges for businesses. One major issue...
Read MoreDEC Alpha hardware has been pivotal to many businesses due to its reliability, performance, and...
Read MoreLegacy application migration is a new trending buzz of IT discussion. Businesses are migrating from...
Read MoreDon't let your legacy systems slow you down! Contact us today and transform your legacy environment into a dynamic, agile platform for success.
Kickstart your journey towards a more efficient and streamlined business environment with just one click.